6 Reasons Why Offsite Backup in the Cloud is 100% Critical to Save Your Business
July 27, 2015/0 Comments/in Blog /by leslie
Many times, businesses suffer not only the financial devastations caused by data loss, but they suffer the loss of client confidence. Both are equally devastating and determine whether a business can survive.The industries that typically suffer the most frequent and expensive breaches are healthcare, financial, pharmaceuticals, transportation and communications. More than one-third of attacks are on businesses with fewer than 250 employees.There’s a lot at risk when a business fails to implement a successful and thorough off-site data backup plan. Some companies never recover from the blow.
After a major data loss, only 6% of those businesses will survive, studies show. A whopping 51% go out of business within two years, while a sober 43% are gone immediately. We all know that off-site data backup is something we should be doing. But, it’s not something that we all do. Cloud backup services are an insurance policy to protect your data from any number of data loss threats. It gives you peace of mind.
Consider the following data loss situations. They are all too common and could send your business down the drain if an off-site backup solution is not in place.
1. Deleting files: Updating files or deleting them are common activities. We often lose data simply because we don’t have proper work-flow procedures and backup strategies. More efficient procedures for saving work and making backups regularly will definitely save time.
2. Viruses & malware: New viruses attack computers every day. Damages greatly differ, but most viruses affect operational systems and damage stored data. Making regular backups of your data and storing the data safely off-site allows you to access it after severe virus attacks.
3. Mechanical damages: Computer hardware is a fragile part of business networks. There are ways to recover data, but this service can be costly. There’s no guarantee you can totally recover your important data. Regular off-site backups help in case of hardware troubles and keeps the latest version of your data in safe storage.
4. Power failures: Power failures affect operation systems and computer hardware. Suddenly shutting your computer or business systems down without proper procedures causes problems. This leads to a chain reaction, and your data is gone. Offsite data backups makes you feel better and more secure, keeping data in a safe place where you can recover it.
5. Computer theft: It’s a tragedy to lose both your computer and data at the same time. While traveling, you may leave your laptop unattended, lose it in an airport, conference center, coffee shop or any other crowded place. New computers cost money, but the data lost is even more expensive. If you use a proper off-site data backup strategy, you can recover your data even after your computer is long gone.
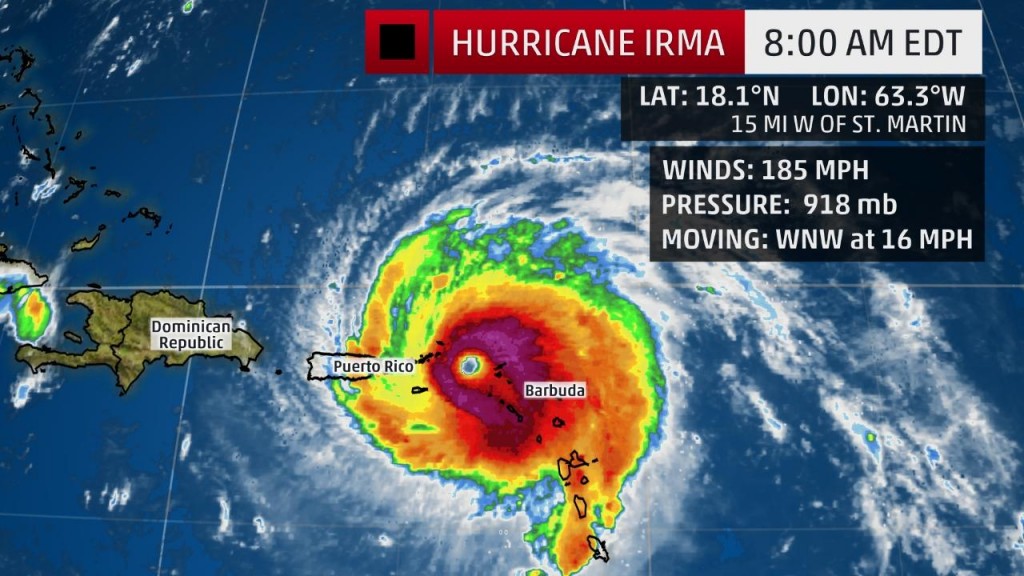
6. Fire & explosions: Explosions rarely happen, but fire mostly likely destroys both your computer and data. Fire is also dangerous when backups are stored in the same location. The safest practice against fire is to make regular backups and keep them in the cloud.
In all these cases, another factor to consider is the cost of data recovery. The cost of professional recovery can be considerably more than maintaining an off-site backup. The best data recovery case is one that uses a reliable, off-site backup solution.
It’s the last stop to preventing complete business failure.



 ne (and become cryptolocked as the malware travels through the network).
ne (and become cryptolocked as the malware travels through the network).